Testing Your OPNsense Setup
TL;DR
Comprehensive verification procedures for your OPNsense setup. Tests everything from basic connectivity to VPN failover, DNS leak prevention, and VLAN isolation.
Prerequisites:
- Completed OPNsense setup
- SSH access
- Test devices
What you’ll test:
- Basic connectivity and DHCP
- DNS resolution and AdGuard filtering
- VPN tunnels, static routes, and failover
- Firewall rules, kill switch, and management access
- NTP redirect and WAN inbound exposure
- VLAN isolation (including reverse isolation)
- DNS, WebRTC, and IPv6 leak prevention
Run tests in order since later tests depend on earlier ones passing. If the kill switch test (5.1) fails, your ISP sees all traffic.
Basic Connectivity Tests
Test 1.1: DHCP Assignment
| Location | Validates |
|---|---|
| Client device on each VLAN | Device receives IP from DNSmasq |
Windows: ipconfig | macOS/Linux: ip addr | Mobile: Settings → Wi-Fi → Network details
Expect:
- IP within your DHCP range (e.g.,
10.0.0.100 - 10.0.0.150) - Gateway matches VLAN gateway (e.g.,
10.0.0.1) - DNS server set to gateway IP
Test 1.2: Gateway Reachability
| Location | Validates |
|---|---|
| Any client device | Device can reach its own VLAN gateway |
ping -c 4 <your-gateway-ip>Example gateways: LAN 10.0.0.1 | SecWiFi 10.0.40.1 | Guest 10.0.44.1 | IoT 10.0.42.1
Expect:
4 packets transmitted, 4 received, 0% packet lossTest 1.3: Internet Connectivity
| Location | Validates |
|---|---|
| Any client device | Traffic reaches internet through OPNsense |
ping -c 4 1.1.1.1Expect:
4 packets transmitted, 4 received, 0% packet lossDNS Resolution Tests
Test 2.1: Basic DNS Resolution
| Location | Validates |
|---|---|
| Any client device | DNS queries resolve correctly |
nslookup github.comExpect:
Server: 10.0.0.1
Address: 10.0.0.1#53
Name: github.com
Address: 140.82.121.3Test 2.2: Local Domain Resolution
| Location | Validates |
|---|---|
| Client device on LAN | Internal hostnames resolve via DNSmasq |
This test requires DNSmasq host overrides configured. See Local Domain Names guide for setup.
nslookup nas.home.byteron.comExpect:
Server: 10.0.0.1
Address: 10.0.0.1#53
Name: nas.home.byteron.com
Address: 10.0.10.50The IP returned depends on your DNSmasq configuration, either a specific host override or wildcard entry pointing to your reverse proxy.
Test 2.3: AdGuard Filtering
| Location | Validates |
|---|---|
| Client device (any VLAN except VLAN46) | Ad/tracking domains blocked |
This test requires AdGuard Home with blocklists configured. See the AdGuard Home configuration guide for blocklist setup.
nslookup doubleclick.netExpect:
Server: 10.0.0.1
Address: 10.0.0.1#53
Name: doubleclick.net
Address: 0.0.0.0AdGuard blocks the domain by returning 0.0.0.0.
Test 2.4: VLAN46 Bypasses AdGuard
| Location | Validates |
|---|---|
| Device on VLAN46 (10.0.46.x) | GoatNET bypasses AdGuard filtering |
nslookup doubleclick.netExpect:
- Returns real IP addresses (not
0.0.0.0) - Browser can load ad/tracking sites
VPN Tunnel Tests
Test 3.1: VPN Tunnel Status
| Location | Validates |
|---|---|
| OPNsense SSH | WireGuard tunnels established and active |
wg showExpect:
interface: wg0
public key: H8mPI4ZE...
private key: (hidden)
listening port: 51820
peer: hf+klJbI...
endpoint: <VPN_SERVER_IP>:51820
allowed ips: 0.0.0.0/0
latest handshake: 1 minute, 50 seconds ago
transfer: 407.93 GiB received, 6.32 GiB sent
interface: wg1
public key: vpDqhKQT...
private key: (hidden)
listening port: 51819
peer: flq7zR8W...
endpoint: <VPN_SERVER_IP>:51815
allowed ips: 0.0.0.0/0
latest handshake: 1 minute, 6 seconds ago
transfer: 320.44 MiB received, 125.80 MiB sentBoth tunnels should show recent handshakes (< 2-3 minutes) and transfer data.
Test 3.2: Exit IP Verification
| Location | Validates |
|---|---|
| Any client device | Traffic exits through VPN, not ISP |
curl ifconfig.meExpect:
194.36.25.XXThe IP should be your VPN provider’s IP, not your real ISP IP. Verify at https://whatismyipaddress.com that the location shows VPN country, not your actual location.
Test 3.3: VPN Gateway Status
| Location | Validates |
|---|---|
| OPNsense Web UI | Gateway monitoring shows correct status |
Navigate to: System → Gateways → Status
Expect:
Name | Gateway | Monitor | RTT | Loss | Status
-------------|--------------|------------|--------|------|--------
WAN_UK_VPN | 10.65.x.x | 100.64.0.1 | 25ms | 0% | Online
WAN_DE_VPN | 10.65.x.x | 100.64.0.2 | 35ms | 0% | Online
WAN_DHCP | <ISP_GW> | <ISP_IP> | 10ms | 0% | OnlineBoth VPN gateways should show Online with low RTT and 0% loss.
Test 3.4: Static Route Verification
| Location | Validates |
|---|---|
| OPNsense SSH | VPN endpoint static routes exist and point to WAN gateway |
netstat -rn | grep -E "185\."Expect: Each VPN endpoint IP routed through your WAN gateway:
Destination Gateway Flags Netif
185.65.135.202/32 <ISP_GW> UGS igb0
185.209.196.77/32 <ISP_GW> UGS igb0Without these routes, VPN tunnels cannot establish due to circular routing — traffic destined for the VPN endpoint gets routed through the tunnel that doesn’t exist yet.
Gateway Failover Tests
Test 4.1: Primary VPN Failover
| Location | Validates |
|---|---|
| Client device | Traffic automatically switches to secondary VPN when primary fails |
- Run
curl ifconfig.meand note the IP (should be primary VPN) VPN → WireGuard → Instances→ Disable UK_VPN → Apply- Wait 30 seconds, run
curl ifconfig.meagain - Re-enable UK_VPN
Expect:
- IP changes from UK to DE VPN location
- Gateway status shows UK_VPN offline
Test 4.2: Gateway Monitoring Response Time
| Location | Validates |
|---|---|
| OPNsense Web UI + SSH | Gateway failures detected within 30 seconds |
- Open
System → Gateways → Statusin browser - SSH into OPNsense and run
service wireguard stop wg0 - Watch gateway status page
- Run
service wireguard start wg0to restore
Expect:
- Gateway status changes to “Offline” within 20-30 seconds
- Packet loss shows 100%
Firewall Rule Tests
Test 5.1: Kill Switch Verification
| Location | Validates |
|---|---|
| Client device | No traffic escapes through WAN when VPN is down |
VPN → WireGuard → Instances→ Disable both UK_VPN and DE_VPN- Run
ping 1.1.1.1andcurl ifconfig.mefrom a client device - From Plex server:
curl ifconfig.me→ Should return your WAN IP - Check
Firewall → Log Files → Live View→ Filter for “Kill Switch” - Re-enable both VPN instances
Expect:
- All client internet traffic fails — no packets reach external IPs
- Plex server still has internet via WAN (floating rule with Quick bypasses kill switch)
- Firewall logs show blocked packets from kill switch rule
Test 5.2: Inter-VLAN Communication
| Location | Validates |
|---|---|
| Multiple client devices | VLANs communicate only as permitted by rules |
Test with ping -c 2 <target-gateway> from each source VLAN:
| From ↓ \ To → | LAN 10.0.0.1 | SecWiFi 10.0.40.1 | DMZ 10.0.10.1 |
|---|---|---|---|
| LAN | — | Pass | Pass |
| SecWiFi | Pass | — | Pass |
| DMZ | Timeout | Timeout | — |
| Guest | Timeout | Timeout | Timeout |
| IoT | Timeout | Timeout | Timeout |
| GoatNET | Timeout | Timeout | Timeout |
Key points:
- LAN and SecWiFi can reach each other and DMZ (
SEC_LAN_IGrules) - DMZ cannot initiate connections back to LAN or SecWiFi (prevents lateral movement)
- Guest, IoT, and GoatNET are fully isolated from all other networks
Test 5.3: Management Access Control
| Location | Validates |
|---|---|
| Untrusted VLANs | OPNsense admin interface unreachable from Guest, IoT, GoatNET, DMZ |
From each untrusted VLAN, test against its own gateway IP:
curl -k --connect-timeout 5 https://<gateway>:443
ssh -o ConnectTimeout=5 root@<gateway>| VLAN | Gateway | Expected |
|---|---|---|
| Guest | 10.0.44.1 | Timeout |
| IoT | 10.0.42.1 | Timeout |
| GoatNET | 10.0.46.1 | Timeout |
| DMZ | 10.0.10.1 | Timeout |
Only SEC_LAN_IG networks (LAN, SecWiFi) can reach OPNsense management ports.
Test 5.4: Port-Based Filtering
| Location | Validates |
|---|---|
| Client device on LAN | Only allowed ports reach internet |
# Allowed port
curl -I https://example.com
# Blocked port
telnet smtp.gmail.com 25Expect:
curlreturns HTTP 200 — common ports (80, 443) worktelnettimes out — port 25 not inPORTS_OUT_WANalias
Test 5.5: NTP Redirect Verification
| Location | Validates |
|---|---|
| Client device | NTP queries redirected to OPNsense, external NTP blocked |
ntpdate -q pool.ntp.orgExpect:
- Command succeeds — NAT redirect catches the query and sends it to OPNsense
- Time offset is small (< 1 second)
Test 5.6: WAN Inbound Scan
| Location | Validates |
|---|---|
| External device (mobile data, VPS, etc.) | Only intended ports visible from WAN |
From a device outside your network:
nmap -sT -p 22,80,443,8080,32400 <your-WAN-IP>Expect:
- Only ports with active NAT port forwards respond (e.g.,
32400for Plex,443for reverse proxy) - Everything else filtered or closed
VLAN Isolation Tests
Test 6.1: Guest Network Isolation
| Location | Validates |
|---|---|
| Device on VLAN44 (Guest) | Internet works, local network inaccessible |
Should work: curl ifconfig.me and ping 1.1.1.1
Should fail: ping 10.0.0.1 (LAN gateway) and nslookup nas.home.byteron.com
Expect:
- Full internet connectivity
- No access to
10.0.x.xaddresses except own gateway10.0.44.1 - Cannot resolve local hostnames
Test 6.2: IoT Network Isolation
| Location | Validates |
|---|---|
| Device on VLAN42 (IoT) | Internet only, no access to other VLANs |
Should work: ping 1.1.1.1
Should fail: ping 10.0.0.1 and ping 10.0.40.1
Expect:
- Internet access works
- Cannot reach LAN, SecWiFi, or DMZ
Test 6.3: DMZ Access Control
| Location | Validates |
|---|---|
| Multiple devices | LAN can reach DMZ, DMZ cannot reach LAN, untrusted VLANs blocked from DMZ |
Test with ping -c 2 <target> from each source:
| Source | Target | Expected |
|---|---|---|
| LAN | 10.0.10.1, 10.0.10.100 | Pass |
| SecWiFi | 10.0.10.1 | Pass |
| Guest | 10.0.10.1 | Timeout |
| IoT | 10.0.10.1 | Timeout |
| DMZ | 10.0.0.1, 10.0.40.1 | Timeout |
Key points:
SEC_LAN_IGnetworks (LAN, SecWiFi) can reach DMZ- Guest, IoT, GoatNET blocked from DMZ
- DMZ cannot reach LAN or SecWiFi (prevents lateral movement if DMZ is compromised)
Test 6.4: GoatNET Isolation
| Location | Validates |
|---|---|
| Device on VLAN46 (GoatNET) | Internet works through VPN, no access to other VLANs |
Should work: curl ifconfig.me and ping 1.1.1.1
Should fail: ping 10.0.0.1, ping 10.0.10.1, and ping 10.0.40.1
Expect:
- Internet access works through VPN
- Cannot reach LAN, SecWiFi, DMZ, Guest, or IoT networks
- Only own gateway
10.0.46.1is reachable
DNS Leak Prevention Tests
Test 7.1: DNS Leak Test (Web)
| Location | Validates |
|---|---|
| Client browser | DNS queries go through VPN, not ISP |
Visit https://dnsleaktest.com and click “Extended test”
Expect:
- All DNS servers belong to your VPN provider
- No servers from your ISP
- DNS location matches VPN country
Test 7.2: DNS NAT Redirect Verification
| Location | Validates |
|---|---|
Client terminal on DNS_ADGUARD_IG network | External DNS queries redirected to AdGuard, not leaked |
The DNS NAT redirect on DNS_ADGUARD_IG rewrites all port 53 traffic to AdGuard on 10.0.0.1. NAT rewriting happens before firewall filtering in OPNsense, so the floating DNS block rule is defense-in-depth for cases where NAT doesn’t apply.
dig @8.8.8.8 doubleclick.net +shortExpect: Returns 0.0.0.0
This proves the query never reached Google DNS — Google doesn’t block doubleclick.net. The NAT redirect caught the query and sent it to AdGuard, which returned 0.0.0.0.
Verify both paths return the same result:
dig doubleclick.net +short # Normal path → should return 0.0.0.0
dig @8.8.8.8 doubleclick.net +short # Redirected → should also return 0.0.0.0If @8.8.8.8 returns a real IP instead of 0.0.0.0, the NAT redirect is broken and DNS is leaking to Google.
Test 7.3: WebRTC Leak Test
| Location | Validates |
|---|---|
| Client browser | WebRTC doesn’t leak real IP |
Visit https://browserleaks.com/webrtc and check “IP Addresses” section
Expect:
- Only shows VPN IP (
10.65.x.xor public VPN IP) - Does NOT show your ISP’s public IP
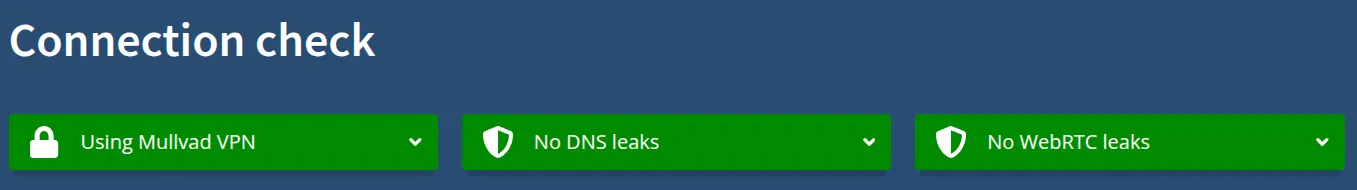
Test 7.4: Mullvad Connection Check
| Location | Validates |
|---|---|
| Client browser | Comprehensive leak test covering DNS, WebRTC, and IP in one check |
Visit https://mullvad.net/en/check
This tool checks everything at once: your IP address, DNS servers, and WebRTC leaks. Even if you’re not using Mullvad VPN, this tool works for any VPN provider.
Expect:
- Green checkmarks across all categories
- IP address shows VPN server location (not your real location)
- DNS servers belong to your VPN provider (not your ISP)
- No WebRTC leaks detected
Test 7.5: IPv6 Leak Test
| Location | Validates |
|---|---|
| Client device + OPNsense SSH | IPv6 disabled, no traffic bypasses VPN via IPv6 |
IPv6 leaks are one of the most common VPN bypass vectors. If a client has IPv6 connectivity and OPNsense doesn’t handle it, traffic goes around the VPN entirely.
ping6 -c 4 2001:4860:4860::8888
curl -6 ifconfig.meExpect:
ping6fails with “Network unreachable”curl -6fails with connection error
Verify on OPNsense SSH:
ifconfig | grep inet6Expect: No global IPv6 addresses. Link-local fe80:: entries are acceptable.
[references] ▸
-
[1.1]
Building a Secure Home Network with OPNsense — Complete OPNsense configuration guide
-
[1.2]
Plex Remote Access Through OPNsense VPN — Configure Plex bypass for remote access
-
[2.1]
Mullvad Connection Check — Comprehensive leak test covering DNS, WebRTC, and IP
- [2.2]
- [2.3]
- [2.4]
[changelog] ▸
- → Added static route, management access, NTP redirect, WAN inbound, GoatNET isolation, and IPv6 leak tests
- → Fixed DNS leak test to verify NAT redirect behavior
- → Expanded inter-VLAN and DMZ isolation tests with reverse direction coverage
- → Added Plex bypass verification during kill switch test
- → Initial publication
Disclaimer
Use the information provided here at your own risk, but if you find errors or issues in this guide, leave a comment and I’ll try to address them ASAP.
Comments